Prelude Research's Red Team Platform
Naturally I was curious about what Prelude Research's Operator actually does, after coming across their Substack page, and I had a play around with it on a Windows laptop.
Simulating a Remote Access Toolkit
Most users of Prelude Operator will probably already know what 'agents' and 'beacons' are, and how they're relevant to Red Team operations, but I haven't covered much in the way of security-related things on my Substack posts yet.
Essentially what Operator simulates is a scenario in which an attacker had exploited a security vulnerability in a target system that enables the installation of malware. In the context of what Operator simulates, this malware is commonly referred to as a 'Remote Access Toolkit' (RAT). This is different to a virus, spyware, ransomware, etc. in that it enables the attacker to control the infected machine, and usually without the owner being aware of it. It could be as simple as a backdoor providing a reverse shell. The how and why it happens is a comprehensive subject area.
A common example is that of an employee within a targetted organisation clicking a link in an email, which starts a sequence of things resulting in the installation of a RAT: the link points to a server that hosts an exploit, the exploit's payload fetches an installer for whatever malware and it runs silently as a background process. Usually this hijacks a program that's already running with admin permissions on the system, which gives the attacker access to everything.
There are other (and more discrete) ways it could happen, but that's the long and short of it, and the result is the same.
Now, in order for the attacker to actually use the malware (i.e. send commands to it, fetch data), s/he will need to know the IP address of the machine it's running on. The malware needs to send that information to a Command and Control (C&C) server - this is known as 'beaconing'. The malware also needs to listen on a predetermined port for incoming commands.
In Prelude's system, Operator simulates the C&C server, and the pneuma agent simulates the remote access malware.
Operator as a Post-Compromise Framework
Setting up Operator assumes the attacker had already gained access to the target system and had installed the malware (or agent), as the docs point out:
While it can be used to conduct initial access, Operator focuses mainly on post-compromise. In other words, it assumes that a bad actor has found their way into your network (i.e., you deploy an agent on a chosen "compromised" computer) and it tests your defenses from that moment forward.
At best, a Red Team running Operator could describe what an attacker could potentially do after gaining access to a system. It wouldn't reveal much about the actual state of a network's defences, or about vulnerabilities that enable an attacker to compromise a system in the first place, and there's no way of knowing with any certainty which (if any) exploits would be used post-compromise.
However, in case studies of Advanced Persistent Threats, we do find examples of attackers using post-compromise exploits to extend access to other systems and make that access more evasive and persistent.
Operator still has a lot of academic value, given its utility as a source of information about common exploits. Aside from being useful for organisations that genuinely are likely targets of APTs, I see Operator being more a tool for Red Teams hacking a Linux box/VM for demo purposes, and for lab sessions in a security training programme.
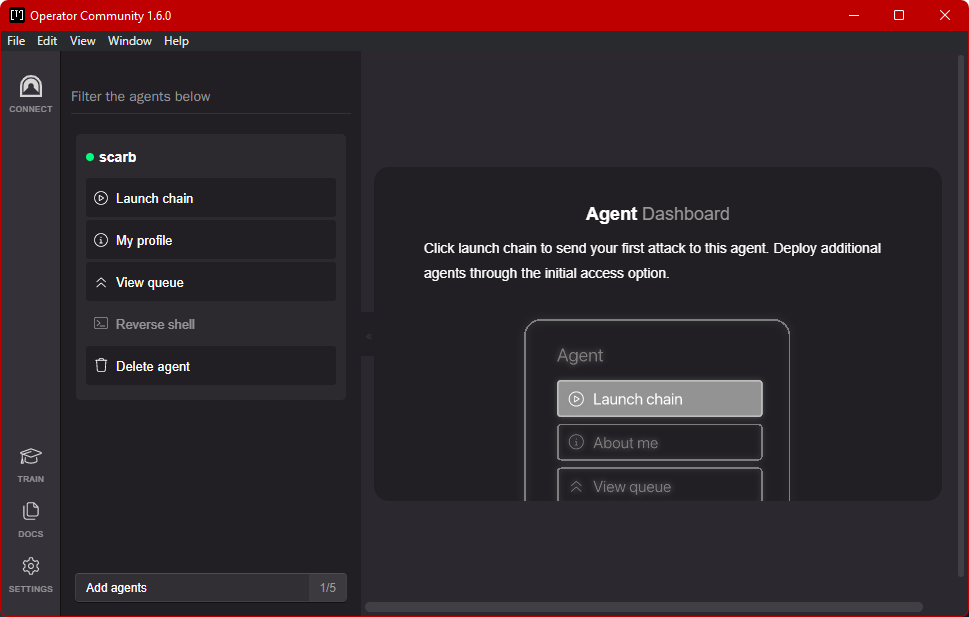
The Agent
The configuration details for pneuma can be found by clicking the 'Add agents' button to the lower-left. The instructions for installing pneuma on a target system are displayed here.
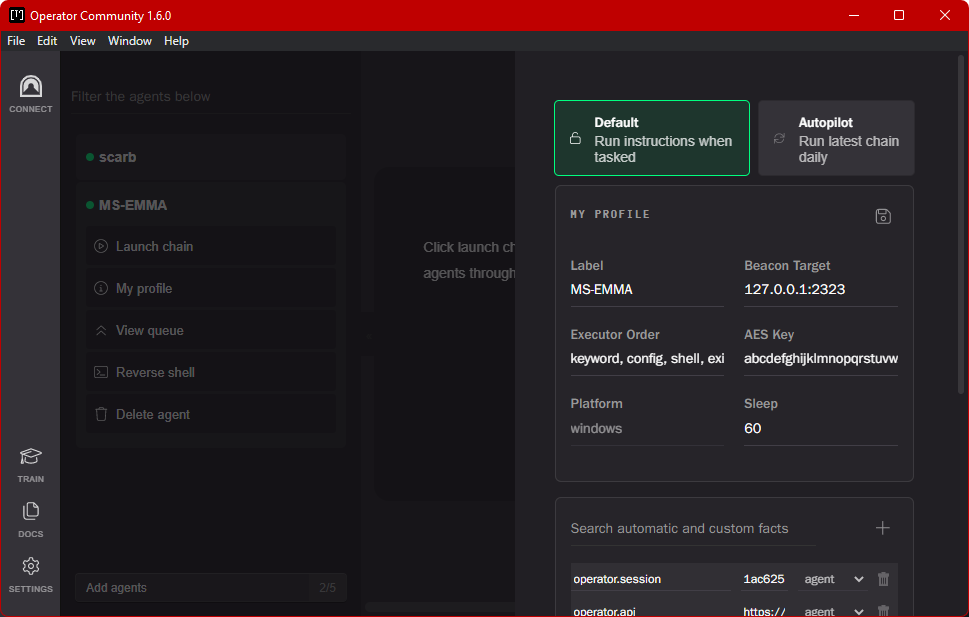
The agent can be used with Operator, or compiled and installed as a stand-alone RAT that will beacon its IP address to a custom C&C server and listen for commands.
Here I've installed pneuma and Operator on the same machine, using the loopback address for beaconing and comms. In Settings, I enabled the HTTPS listening post plugin, and set the Agent Callback Address to localhost.
In the 'Add agent' window, I set the address to localhost and run the script to install pneuma. If anti-malware is enabled on a Windows machine, PowerShell will detect it as malware (though incorrectly identify it as a virus). Since security must be disabled, I still recommend only running it on a VM.
After installation, pneuma beaconed its presence, and a new section and profile appeared for the machine its running on.
From that point, the agent can run any of the numerous exploits available, but what I'd be interested in, as an attacker, is the reverse shell - access to the command line on the target machine. As expected, this what Operator provides.
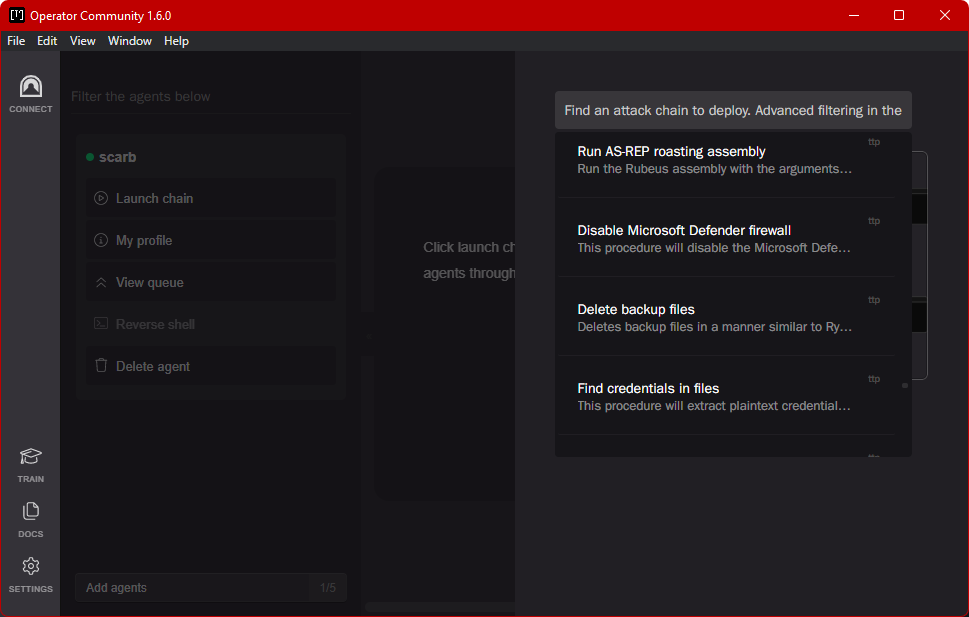
TTPs
Under the 'Launch Chain' tab, Operator will list various attacks and exploits. Just to name a few categories, there are TTPs for:
Data collection
Command and control
Privilege escalation
Exfiltration
Discovery
These are read from a repository of .yaml files, which I think are read and run by the agent. Some of them contain references to TTP, CVE and MITRE information, and pointers to what other security researchers had published. If the file refers to an exploit, the file will include the commands for compiling and executing it.
For more advanced things, a sequence of TTPs can be executed as a Launch Chain.
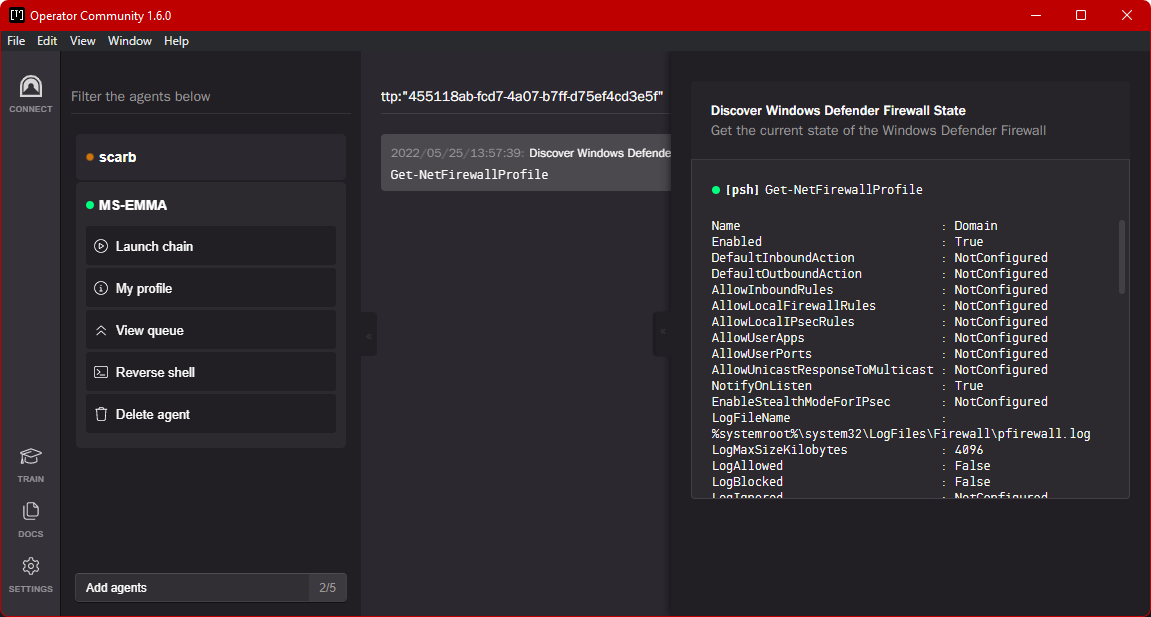
Just to give it a try, I selected something that would run on a Windows system and likely wouldn't damage anything damage - 'Discover Windows Defender Firewall State'. I clicked 'Deploy'.
Cleaning Up
This is important! Click the option to delete the agent, then make sure the Windows Security is enabled on the target machine.